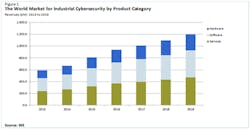
IHS projects a "good but not spectacular" growth rate for industrial cybersecurity hardware, software and service revenues, with an annual average growth rate of 12 percent from 2013 to 2019. The market will be sustained by the high number of legacy assets that require securing, IHS reports. Over a much longer 10- to 15-year timeframe, the demand for on-top hardware/software/services is likely to decrease, however, as fewer compensating controls will be required to secure control systems that are secure by design.
IHS senior analyst Toby Colquhoun says the overall market for industrial cybersecurity products remains extremely immature, with currently over 160 vendors offering a wide variety of hardware, software and services. In contrast to other parts industrial automation markets, no one vendor dominates; and those with the highest market share typically specialize in a particular region, industry sector or technology. IHS believes there will be a “shakeout”—although the market will attract some new entrants, this will be largely offset by companies choosing to exit the business and by acquisition-driven consolidation.
Control systems already in use will sustain the market for “on-top” industrial cybersecurity hardware, software and services, IHS reports, explaining that control system upgrades are expensive and must be kept in place for many years to show a return on the investment and many of these systems are inherently insecure.
READ ALSO: Fundamental Cybersecurity Strategies for Effectively Securing Your Process Systems
Colquhoun says a “quiet revolution” is already occurring in an industry more used to incremental improvement. Vendors of control systems have united around IEC 62443 (the international version of ISA-99) which, when finalized, will describe how to secure control system assets throughout their lifecycle (including development). Whereas security was an afterthought in earlier generations of control systems, asset owners have pushed suppliers to restructure their products to implement security features that provide some inherent levels of protection. Only parts of the IEC 62443 standard have so far been released; but once the standard and certification services are available, all tier 1 vendors are expected soon to offer an IEC 62443 product, Colquhoun says.
It is likely that these products will have different levels of capability, says Colquhoun. IEC 62443 has seven major criteria for building secure components/systems. For these criteria, the IEC 62443 standard borrows some of the language of the safety world—the security levels “SL” are analogous to safety-integrated-levels, with levels ranging from 1 to 4 (SL 1 being least secure, SL 4 being most secure) although the final security level depends on how the asset owner implements the component or system.
The largest “known unknown” remains legislation, Colquhoun says. IHS believes that legislation affecting the process and discrete industries is unlikely.
“The effect of investment on profit is also a concern: the oil industry (both upstream and downstream) is one of major spenders on industrial cybersecurity products, as the high price of oil can support investment,” Colquhoun says. “However, the water industry, despite its importance to society, is not a major spender on these products, as it comprises smaller companies with prices often set by regulators.”